As the interminable financial crisis persists and threats of terrorism, vandalism and theft pervade, demands are increasing for efficient and intelligent perimeter systems to better protect assets and people. A&S International takes a closer look at implementing different levels of perimeter security and factors that need to be considered before making purchasing decisions.
As the interminable financial crisis persists and threats of terrorism, vandalism and theft pervade, demands are increasing for efficient and intelligent perimeter systems to better protect assets and people. A&S International takes a closer look at implementing different levels of perimeter security and factors that need to be considered before making purchasing decisions.
The global financial crisis coupled with subsequent waves of terrorist attacks have  prompted tremendous action to be taken to strengthen perimeter security on varying fronts depending on sites of employment. Price hikes in a number of valuable natural resources have also resulted in increasing needs for perimeter protection to prevent theft and terrorist actions.
prompted tremendous action to be taken to strengthen perimeter security on varying fronts depending on sites of employment. Price hikes in a number of valuable natural resources have also resulted in increasing needs for perimeter protection to prevent theft and terrorist actions.
"Terrorist events perpetrated in Spain, Morocco, Algeria, the United Kingdom, as well as the recent incursion of Russian forces into Georgia, have further intensified the demand for border and sovereign critical infrastructure protection,” stressed Nicolas Jdanoff, Overseas Sales Manager of Sorhea.
Perimeter security systems for critical infrastructure, oil/gas refineries, embassies, prisons, utilities and petrochemical sectors (regulated in the United States by Public Health Security and Bioterrorism Preparedness and Response Act 2002) are forecasted to climb to billions of U.S. dollars in the next five years (www.homelandsecurityresearch.net ). One can only imagine the enormity of employing appropriate systems that deter, identify, assess and track unauthorized intruders from stepping into the boundaries of secured perimeters.
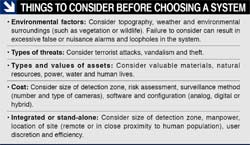
As protecting strategic assets becomes ever more important, so must perimeter  providers manage increasing demands by providing appropriate choices for users' varying needs. “These needs include size of detection zone, likelihood of detection and intrusion, risk assessment, false-alarm rates, nuisance alarm rates, capability of integration and relevance of natural obstacles like weather and cost,” said Steve Kovacs, Director of Business Development for Zareba Security.
providers manage increasing demands by providing appropriate choices for users' varying needs. “These needs include size of detection zone, likelihood of detection and intrusion, risk assessment, false-alarm rates, nuisance alarm rates, capability of integration and relevance of natural obstacles like weather and cost,” said Steve Kovacs, Director of Business Development for Zareba Security.
Despite differences in selection criteria, the goal is to detect, assess and apprehend well before a potential threat unfolds no matter what systems are employed.
Protection at a Physical Level
Though basic and traditional, perimeter solutions at a physical level remain extremely useful and cost-effective. Physical taut wire systems protect valuable assets and property, primarily for military, industrial and infrastructure sites.
"Taut wire systems have a 99.9-percent detection range and are cost-effective  when employed over a large perimeter,” said Kovacs. “These systems are also excellent physical deterrents.”
when employed over a large perimeter,” said Kovacs. “These systems are also excellent physical deterrents.”
Oil refineries, water treatment facilities and military bases have made physical perimeter security a necessity, particularly because it has extremely low nuisance alarm rates (since a significant amount of force is needed on the wire to trigger alarms) and can withstand weather and topographic complications that more sophisticated technologies alone cannot.
Other developments see taut wire systems employing sensors on a wire array in small increments (every 20 to 40 feet), with microprocessors located in each sensing post that communicate to the head-end via outdoor cables or fiber optic backbones, said Kovacs. This increases the system's identification and assessment capabilities because when an alarm is set off within small increments of 20 feet, users can find the area of intrusion quickly and efficiently. Furthermore, alarms for taut wire systems can now be configured to filter out nuisances created by weather, blowing vegetation or small animals, said Kovacs.
"Detection fence solutions can be implemented both actively and passively; for structurally particular sites where fences are not suitable, explosion-proof windows and security walls are also effective deterrents,” said Fredrik Granat, GM of Gunnebo.
Perimeter fence intrusion detection systems should be able to provide electrified mode on wire arrays for deterrence for high security measure facilities, said Chris Bae, Marketing Manager of GDI. Fence mounted sensors will detect cut or climb  attempts and the latest technology can accurately locate the point of an intrusion attempt to within three meters, said Tom Wallace, National Sales Manager of the Security Systems Division of Southwest Microwave.
attempts and the latest technology can accurately locate the point of an intrusion attempt to within three meters, said Tom Wallace, National Sales Manager of the Security Systems Division of Southwest Microwave.
Combining Intrusion Detectors
Sites with larger perimeters — including airports, seaports, nuclear power plants, military bases and industrial sectors — generally combine two or more intrusion
detectors on top of physical barriers to deter and assess intrusion.
"Intruders identifying the presence of these devices will more likely avoid the property, and those who activate the system will also more likely be scared away  by alarms before gaining access,” said James Ludwig, Managing Director of Texecom.
by alarms before gaining access,” said James Ludwig, Managing Director of Texecom.
Popular intrusion detectors include microwave sensors, active IR beams, outdoor PIR motion sensors, mirrored optics, kinematic detectors, fiber optic detection cables and so on.
"Microwave barriers are increasingly used to protect high-risk sites because false-alarm rates are very low, even under extreme weather conditions,” said Fabrizio Leonardi, Marketing and Communications Director of CIAS Elettronica.
So popular are these microwave into the realm of residential sites. “Our engineers have developed a unique solution — microwave detectors camouflaged in garden
lamps,” said Ramunas Brazinskas, Deputy Director of Forteza.
However, microwave sensors may be disrupted by ongoing activities near detection zones, while active IR beams are not. “Active IR beams can be implemented between narrow fence lines and buildings, while other intrusion  detection sensors cannot, for lack of space or infrastructure,” said Jdanoff.
detection sensors cannot, for lack of space or infrastructure,” said Jdanoff.
Two key advantages come from using combined intrusion detection systems. First, each type of sensor responds to different agents, accounting for a wider range of environmental nuisances, said Sebastiano Vento, Export Sales Manager of Sicurit Alarmitalia. Secondly, dual systems often require a simultaneous offset of sensors in both detection areas to activate the actual intrusion alarm, raising the bar to filter out weaker alarm signals, said Ludwig. As such, perimeters are equipped with a more precise pinpointing of the location of intrusion. “Nuisance alarms caused by animals, moving foliage or environmental disturbances produce weaker signals and are ignored,” stressed Ludwig.
Kinematic sensors measure the kinematical behavior of structures that set off alarms if a structure is pushed beyond its parameters, and can be installed to ignore environmental disturbances like wind, said JP Hobbs, Marketing Director of Teqcon (Moduteq). “Kinematic detection sensors and fiber optic detection cables  can be applied to structures such as welded mesh, chain link mesh and palisade fencing. Fiber optic cables can also be embedded in trenches underground,” continued Hobbs.
can be applied to structures such as welded mesh, chain link mesh and palisade fencing. Fiber optic cables can also be embedded in trenches underground,” continued Hobbs.
"Today's buried cable detection systems are terrain-following, offering maximum flexibility for sites with variation in site terrain,” said Wallace. With a combination of
available intrusion detectors, several aspects of the perimeter can be effectively covered.
Sites ranging from educational, to military, industrial, correctional facilities, national borders and even residential homes utilize combined systems. Some global perimeter intrusion detection providers include Teqcon (Moduteq), Texecom, Sicurit Alarmitalia, GDI, CIAS Elettronica, Gunnebo, Sorhea, Forteza, Gallagher Security Management Systems, Southwest Microwave, Magal Security Systems, Senstar and FiberSensys.
Integration with Surveillance Systems
"The main challenge with outdoor perimeter intrusion detection systems is understanding the pros and cons of the different sensor technologies that are available, and then choosing those that best suit the specific site conditions, climate and threat scenario. When properly designed and augmented with appropriate video verification systems, it is possible to provide excellent perimeter security," said Stewart Dewar, Manager of Product Marketing for Senstar Canada. “Many perimeter security providers have developed their products from analog to digital, enabling easy integration into management software,” said Vento.
“Many perimeter security providers have developed their products from analog to digital, enabling easy integration into management software,” said Vento.
Developments in the design of physical perimeter systems show more and more physical barrier systems being linked to surveillance systems for alarm verification purposes, considerably increasing the demand for quality and integrated system designs, said Ludwig. For critical sites, an integrated system of physical barriers
and intrusion detectors with surveillance systems (video analytics, continuous-wave [CW] illumination, thermal imaging or radar video surveillance) must be in play.
A range of high-end technology exists today that caters to these particular needs to maximize the impenetrability of sensitive perimeters. “Airports, for example, have done well to manage the security of people inside the facilities against terrorists, using sophisticated explosive detection,” said Ron Austin, Director of Business Development of HGH Infrared Systems. “The perimeter is the final area that needs to be considered.” Intrusion into restricted areas needs to be strengthened with video surveillance and measures taken to prevent or quickly intercept intrusion.
CW Illumination
"Some airports have multiple incidents per year involving people gaining access to restricted areas,” said Austin. At airports, national borders and sensitive critical
infrastructure where intruders need to be clearly identified and assessed,  cameras with CW illumination are employed. This technology produces near-optical contrast imagery, in which markings can be read and people recognized from zero light (nighttime) to full daylight, said Randall Foster, cofounder, CEO and President of Vumii. CW illumination has incredible implications for perimeter identification and assessment purposes, overcoming light compromises and improving visual clarity.
cameras with CW illumination are employed. This technology produces near-optical contrast imagery, in which markings can be read and people recognized from zero light (nighttime) to full daylight, said Randall Foster, cofounder, CEO and President of Vumii. CW illumination has incredible implications for perimeter identification and assessment purposes, overcoming light compromises and improving visual clarity.
"This approach gives security professionals the familiarity of continuous zoom, high magnification optics 24/7 and the ability to identify targets, see through glass windshields, recognize facial features and read license plates and ship identification numbers at distances of up to 3,000 meters,” said Foster.
Using CW illumination to achieve better target acquisition and tracking under ordinary weather conditions may deliver excellent results; rough weather, however, negatively impacts its performance because particles in the atmosphere obstruct the view of CW illumination.
Thermal Imaging
Thermal imaging (less influenced by weather conditions) can be used to monitor the perimeter and long distances outside the perimeter at similar sites of airports, industrial sectors and critical infrastructure. Current thermal imaging perimeter  systems adhere to the standard IP 65 water- and weather-proof rating.
systems adhere to the standard IP 65 water- and weather-proof rating.
While thermal imaging cameras cannot identify individuals as well as visible-light cameras or CW illumination cameras, they can detect intruders from a distance of one to three kilometers in total darkness, through fog, smoke or hazy atmospheric conditions, said Austin.
New developments in thermal imaging help deliver 360-degree panoramic images and operate auto detection and motion-tracking alarms as well as an area-of-interest zoom, said Austin. Thermal imaging cameras like those of HGH Infrared Systems can be integrated with software designed with automatic detection of intrusion, which operates by "learning” the scene with user-definable parameters, making such products "intelligent.”
Video Analytics
For sites that need to identify, assess and track intruders, integration with intelligent edge devices such as megapixel cameras embedded with video analytics offers a comprehensive solution. “Intruders can be tracked across camera scenes and even from camera to camera if their scenes overlap,” said Rustom Kanga, CEO of iOmniscient. “Technology today is not yet able to track a person across non-overlapping camera views but research is currently under way to address this issue.”
Systems using PTZ cameras are easily defeated by criminals who use decoys to get the camera to look one way while they act on the other side. "Megapixel cameras with the right software have the ability to make multiple detections and  identifications while maintaining detection on the whole scene,” continued Kanga. iOmnicient's video analytics use nuisance alarm minimization systems to detect the difference between light, shadow, waving leaves on a tree, rippling or reflective water, and real objects of intrusion.
identifications while maintaining detection on the whole scene,” continued Kanga. iOmnicient's video analytics use nuisance alarm minimization systems to detect the difference between light, shadow, waving leaves on a tree, rippling or reflective water, and real objects of intrusion.
"Detection is only the first step in addressing an intrusion. The next step is identification using facial and license plate recognition systems. The latest systems can do both at the same time on the same camera,” explained Kanga. Furthermore, intelligent edge devices can be set to detect humans and ignore environmental nuisances like birds flying in the camera's field of view, said Dvir Doron, VP of Marketing for ioimage. This is particularly useful for large sites located in remote areas that frequently encounter environmental nuisances.
What is perhaps the most useful aspect of video analytics aside from its ability to identify and assess intruders is its ability to track them, giving security personnel a more sophisticated and informative understanding of at tempted intrusion. Other than recognizing faces or writing, when video analytics mark and keep track of the path intruders take, end users have the chance to back track, map out the intruder's trail and uncover crucial information otherwise lost to other types of intrusion detection.
Intelligent edge devices like those of ioimage and iOmnicient are known for their  plug-and-play characteristics. Edge devices with intelligent video components built inside are relatively simple to install. "With a ‘plug-and-play' approach, this type of solution is accessible to both the IT savvy security systems integrator and the dealer implementing his first video analytics solution," explained Doron.
plug-and-play characteristics. Edge devices with intelligent video components built inside are relatively simple to install. "With a ‘plug-and-play' approach, this type of solution is accessible to both the IT savvy security systems integrator and the dealer implementing his first video analytics solution," explained Doron.
Integrated systems today include more than just hardware combined with intelligent software; different levels of perimeter security are increasingly being joined to create the strongest barrier possible. As Chris Bone, Security Sales Leader EMEAI of Honeywell Building Solutions said, “Integration is a key differentiator. It brings different security and life safety management applications together onto a common platform — the fusion of sensors to provide 24/7 real-time situational awareness.”
This calls for systems and products to be openly designed, expected to be a part of but not wholly consuming the operation of a perimeter security system. As such, state-of-the-art cameras with video analytic solutions can be used in combination  with one another as well as with complementary intrusion detectors such as microwave sensors to provide safeguards and ensure that any one failure point does not completely degrade the protection of the facility, said Bone.
with one another as well as with complementary intrusion detectors such as microwave sensors to provide safeguards and ensure that any one failure point does not completely degrade the protection of the facility, said Bone.
Central Management Software
Together, intrusion detection and surveillance systems backed with intelligent software can very likely make a perimeter virtually impenetrable.
"n the end, any project cannot be just about the accuracy and efficiency of a sensor; it comes down to how you manage the system and provide accurate information,” said Adam Rosenberg, VP of Marketing for Magal Security Systems. Using up-to-date central management software (CMS) to manage physical barriers, sensors, cameras and other points of relevant security such as access control gives users a complete picture — location of intrusion, relevant information (facial recognition), and what the scene of intrusion looks like.
In real life, CMS allows users to extract necessary information, take that information with video then dispatch it to patrol cars. “This not only gives patrols a picture of the incident and where it was taken, but also a map to guide patrols to the location,” said Rosenberg.
Market Outlook
Struggling with today's financial crisis, security companies are expecting lower growth rates for the second half 2008. However, according to Homeland Security
Research, despite the global financial and economic crisis, homeland security  markets will grow, said Bae.
markets will grow, said Bae.
"Over the last five years, we've seen a significant increase in visitor numbers at trade events, with specific project requirements for perimeter protection, and we anticipate that these needs will continue to escalate,” said Wallace. “Additionally, we're also seeing an increase in sector-specific conferences focusing on the security challenges facing particular groups like water, power and petrochemical industries.”
Aside from high- risk sites, educational areas and research facilities are increasingly taking perimeter security measures such as installing fences linked to surveillance systems, said Bae. More and more users are turning their interests toward perimeter protection because it is  necessary and can be applied to all. "Primeter protection is an advanced warning system that offers end users the increased response time to preempt a threat before it escalates to a potentially catastrophic incident,” said Wallace.
necessary and can be applied to all. "Primeter protection is an advanced warning system that offers end users the increased response time to preempt a threat before it escalates to a potentially catastrophic incident,” said Wallace.
Given the breadth and depth of user needs and particular site demands, the responsibility to provide and administer appropriate and effective perimeter systems falls squarely upon perimeter solution providers.