With an increasing number of devices coming online, the need to ensure cybersecurity is at an all-time high.
With an increasing number of devices coming online, the need to ensure cybersecurity is at an all-time high. But so far, despite major efforts from solution providers, security remains a reactive measure to a large extend. This is especially so because the nature of threats continues to expand and the number of issues that security professionals have to deal with on a daily basis keeps rising.
This is where solutions that help in proactively avoiding security breaches become relevant. The San Jose, CA-based the company,
Balbix, has come up with a predictive breach-risk platform that leverages the power of artificial intelligence (AI).
According to Mark Weiner, Chief Marketing Officer at Balbix, with most current solutions, security staff and SOC personnel face an overwhelming number of incoming alerts and are stuck with tools that are completely reactive and do not prioritize one risk from another (even as 1000s of risks are accumulated over just a few days).
“And as the landscape of attack surfaces continually expands (e.g. cloud, IoT, etc.), the number of unprioritized alerts is only going to continue to grow, and security professionals who are already scarce in number are going to fall even further behind,” Weiner said. “The growth of the problem – and lack of prioritization – outpaces security teams’ ability to add people to address it.”
Proactive measures, better protection
Balbix BreachControl uses deep learning and other advanced AI to maintain a real-time, comprehensive inventory of a customer’s IT assets and users, both on-premises and in the cloud/IoT. Incoming indicator of compromise (IOC) and external threat data is analyzed holistically, incorporating insights from the continuous analysis of vulnerabilities and business impact for the various components of the extended enterprise network.
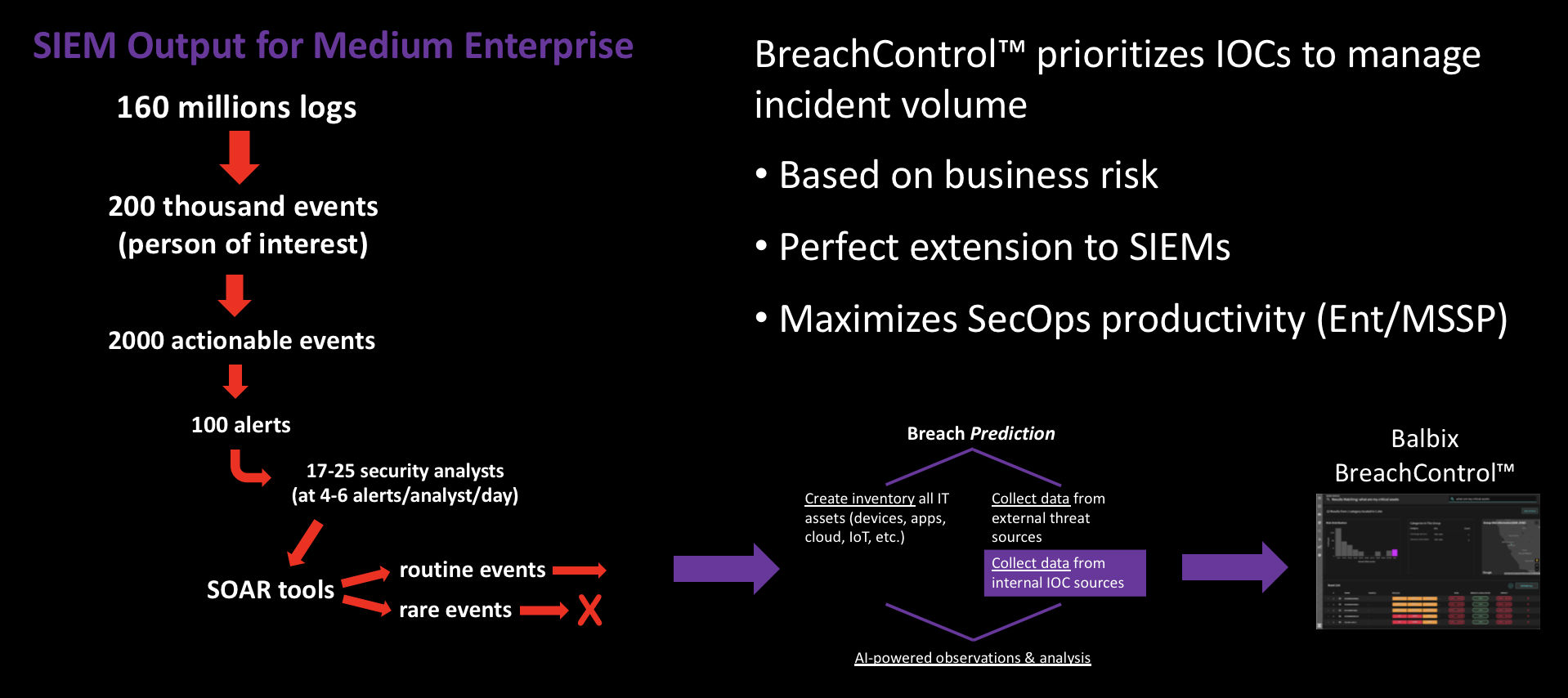 Image source: Balbix
Image source: Balbix
“The result is a complete list of prioritized actions, based on business criticality, that security operations center (SOC) analysts and security staff can take to proactively control risk, avoid breaches and improve resilience + compliance,” Weiner said. “Balbix gathers this expanded set of internal and external data multiple times a day automatically—a stark contrast to traditional vulnerability management tools whose scans are generally run monthly and require security experts to interpret and direct the results.”
The solution helps security teams avoid breaches by proactively predicting breaches, prioritizing actions to address them (based on business risk) and prescribing very clear fixes for each action – across a comprehensive list of 100+ attack vectors. It is visualized via a searchable and clickable risk heat-map designed specifically for CISOs, CIOs, and IT security teams. By forecasting critical breach scenarios and prioritizing/recommending fixes, it improves security operations, compliance, and cyber-resilience.
Weiner added that these capabilities enable enterprise security teams and managed security service providers (MSSPs) to achieve greater impact and risk reduction.
Who is the Customer?
From the customer’s perspective, solutions that seek to remain a step ahead of cyberthreats is indeed appealing. As more and more security and non-security devices go online, such measures would become inevitable. Speaking about Balbix’s market strategy, Weiner said that targeting mid-size to large enterprises and MSSPs initially in North America, but the company’s reach has expanded globally through strategic partnerships with Information Systems Integration and Tech Mahindra.
The company also plans continued extension and application of AI and deep learning to address the challenge of growing attack vectors and types, in the future.
“The customers can also anticipate us taking steps to extend breach avoidance from end-to-end,” Weiner said. “Collaboration with other security vendors through new platforms such as the nascent SOAR (security operations analysis and reporting), which is a logical extension of our initial set of capabilities for integration with SIEM and firewall vendors.”