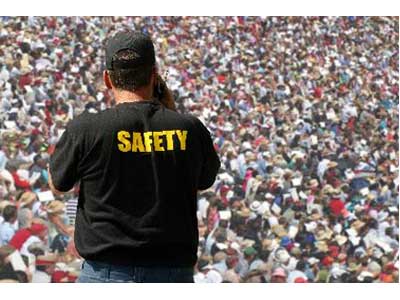
The importance of safety and security at large-scale events is escalated since such events are often high profile in nature, garnering nationwide, if not worldwide attention.
Security planning for large-scale events should be meticulous and detailed as they strike as obvious targets for terrorists due to the significant amount of attention centered on these events from the large number of spectators, the high volume of attendants and participants, and the enormous difficulty to keep any situation under control. Security service providers must conduct proper risk analysis of the location, based on past event history and possible risk factors and risk scenarios that can occur. Allotting enough time to put the plan to action and conduct training and simulations of the event can greatly increase the safety level as well.
Large-scale events range from concerts, awards, rallies, conferences, sports events, etc. Sports events, especially, are no strangers to acts of terror. One of the most notable examples is the 1972 Olympics in Munich, Germany, where the Israeli national team was taken hostage by terrorists and 11 members of the team were slaughtered. Other major attacks seen in sporting events include the bombing in Atlanta's Centennial Olympic Park in the 1996 Olympics in the U.S. and a terrorist bomb that greatly damaged Stockholm's Olympic Stadium in 1997 in Sweden. The recent heart-wrenching Boston Marathon bombing in mid April and the ruthless quartering and decapitation of a referee by angry fans at an amateur soccer match in Brazil in late June this year are added to the growing list of tragedies that have occurred in sporting events.
To encourage the awareness of sports security in the U.S., the National Center for Spectator Sports Safety and Security (NCS4) is offering Sport Event Security Aware (SESA) certifications to all professional, collegiate, and amateur organizations that own or operate sports facilities. Though it is impossible to guarantee zero loopholes when securing a large-scale event, participating in such certification programs can increase the chances of identifying possible risks to ensure they are handled properly.
Risk Analysis
When performing the risk analysis of any event, all forms and factors of possible risk scenarios that can occur must be considered. Some of these include, but are not limited to:, demonstrations; terrorism; loss of key resources; loss of power; loss of money; theft; blackmail; sabotage; hooliganism; transport failure; kidnapping; hijacking; bad weather conditions. “It can be very difficult to classify events for security purposes. Typically, only the highest profile events have the resources required to address all of the security challenges posed. However, there are some standard planning principles applicable to all events.. These include plans for managing known threats and risks, accreditation, access control, asset protection, loss prevention, screening persons and items for restricted and prohibited items, crowd control and crowd management, safety, and others,” advised Kirk Rhodes, Director of Security Projects at P4 International. “In addition, an intelligence-led, risk-based approach to security planning is useful. Considerations include previous history of security-related incidents at each type of event, precedents that have been used for similar types of events, assessment of current intelligence from all available sources including law enforcement and public safety officials, event organizers, governing bodies, sponsors, attendees, presenters, etc., and the collection and analysis of security/crime-related information specific to the event location.”

“The main differentiators between events are not related necessarily to the type of events but are driven by the risk analysis,” said Hagai Katz, Senior VP of Marketing and Business Development at Magal S3. Thus, it is best to make scalable plans as chances are, something will not go according to plan and the security staff must be able to improvise and handle the wide range of events that could possibly happen. The settings of an event – whether it is indoors or outdoors – should be paid attention to, as its location will determine its ease of access by those who are either welcomed or unwelcomed. The neighboring properties and/or facilities should also be taken into consideration depending on what kind of facilities or businesses they are, as sometimes, integration between the two places might be required to better ensure a foolproof security plan. The interest level and exclusivity of the event is another major aspect to pay attention to. Interest level can be divided to specific, local, regional, national, and international. The exclusivity refers to how limited the tickets are, which will give event holders a rough idea of the number of attendees. Posing as another major risk factor is the event staff or workforce supply that will be enlisted to work the event. In some instances, one staff member will be assigned to every 100 attendees, more or less depending on the type of event. When alcoholic beverages are served at such events, it can be guaranteed that the staff-to-spectator ratio will be greatly reduced (i.e. 1:250 for non-alcohol and 1:50 for alcohol) as chances of disorderly conduct, violence, and chaos is escalated with the introduction of alcohol. Their background information and criminal history should also be clean of all delinquent activities.
Planning
Starting early allows time for the security systems to be tested for any bugs and allows security staff to receive all proper training, while allowing time for security procedure rehearsals. “For a large event, it is better it starts four years before; however, we have managed as an example to complete a mega-event project within eight months,” said Katz.
 Permanent vs. Temporary
Permanent vs. Temporary
Depending on the location and duration of the event, security equipment or devices installed or set up for the event can be bought or leased . “For example, in Singapore, the Formula 1 race is a temporary circuit for the F1 cars to race down the fast lane. In this instance, equipment is usually lease-based where they are only deployed during the couple of days the event takes place, which is not that often. We see that most permanent event facilities like stadiums will have fully purchased the equipment because physical security is a long-term need for the facilities and owning it will reduce the cost of ownership of the equipment over time,” said Sunny Kong, Director of Sales in Asia for Milestone Systems.
However, for equipment that is bought or will be permanent installations, event holders and security service providers should hold preliminary discussions about their usage and purpose after the events are over. For this reason, wireless and mobile surveillance and communications products are often suggested as these allow for the flexibility to be used for other purposes after the event is over. “The Bureau of Justice Assistance suggests using video surveillance in the form of wireless and wired cameras, high-definition backpack cameras, and cameras on cellular phones to provide law enforcement with real-time information sharing and situational awareness,” stated Guy Savage, Business Development Executive at Danner's Security. “Whenever possible, wireless systems were installed for the African Cup Games. Without the dependence on wired backbone, these systems were easily relocated to other sites,” added Katz. Venue owners and security companies should consider building “capacity into permanent venue systems to minimize the cost of adding temporary devices to support events,” advised Rhodes. “Learning the art of temporary installation and de-installation will greatly help those security companies responsible for delivering systems in the event environment.”
Policies and Procedures
When defining security perimeters, it is vital that all security staff and personnel are aware of the area of security responsibility, for example areas where the public is allowed access and areas only authorized personnel are allowed to access. All points of entry to the venue should be carefully guarded with radio communication between all staff and emergency responders. All vehicles, bags, carriages, trolleys, etc. must be subjected to careful screening with proper devices so prohibited items and dangerous compounds cannot be brought into the facilities. In fact, many different venues, such as the University of Notre Dame, have started to implement policies where large bags, such as tote bags and duffel bags are no longer allowed into its football stadium. For other events, such as many Independence Day festivities that took place across the U.S. allowed only clear bags where objects inside can be easily identified.

Oftentimes at large-scale events, effective — but temporary — organizational arrangements and management structures must be arranged. It must be stressed that security companies can properly assess the number of staff that will be required for the event and provide enough trained personnel to handle it. The London Olympics of 2012 had been greatly criticized because G4S was unable to provide the number of trained security staff in time for the mega event, and the British government was forced to step in and deploy military personnel of their own to guarantee the safety of the participants and spectators at the event.
Recent Warnings
Due to the recent disasters in large-scale events, security services providers are starting to take extra precaution when performing risk analysis and planning. Planning early and having a scalable system allow the needed adjustments to be discovered and made in time prior the event. Clear protocols for any forms of emergency and disasters should be properly relayed to all members of the security staff and personnel. Communication and coordination is essential among the security staff. Any small mistake can compromise the safety of the crowd.